GXPN: SANS SEC660 Course Writeup
I recently completed SANS SEC660 and gained the GXPN certificate. This is a quick writeup of the course, highlighting the structure, content and my thoughts in general on the whole experience.
Prerequisites
There are no formal prerequisites but SANS recommend having good fundamentals of penetration testing and some experience in any programming language.
I came into it with OSCP, OSWE, some computer science study and a few years of pentesting experience and felt comfortable all the way through. The course does a great job of quickly getting you up to speed on each topic, so if you have good overall fundamentals but the odd blind-spot like crypto or debugging, don’t let that stop you from jumping in.
Format
The course is either:
- live, in-person (a week in situ in a classroom)
- live, remote (joining live classes remotely), or
- on-demand (pre-recorded video classes)
I chose the on-demand version as the content looked like a lot to take in over a week. I also knew I’d want to take it hyper-slow for some of the more complex stuff like stack smashing. Overall I’m happy with this choice - I think it’s the best for me personally, although if you’re more inclined towards in-person learning I think it would be a great choice as you can fire questions at the instructors directly and learn from your classmates too.
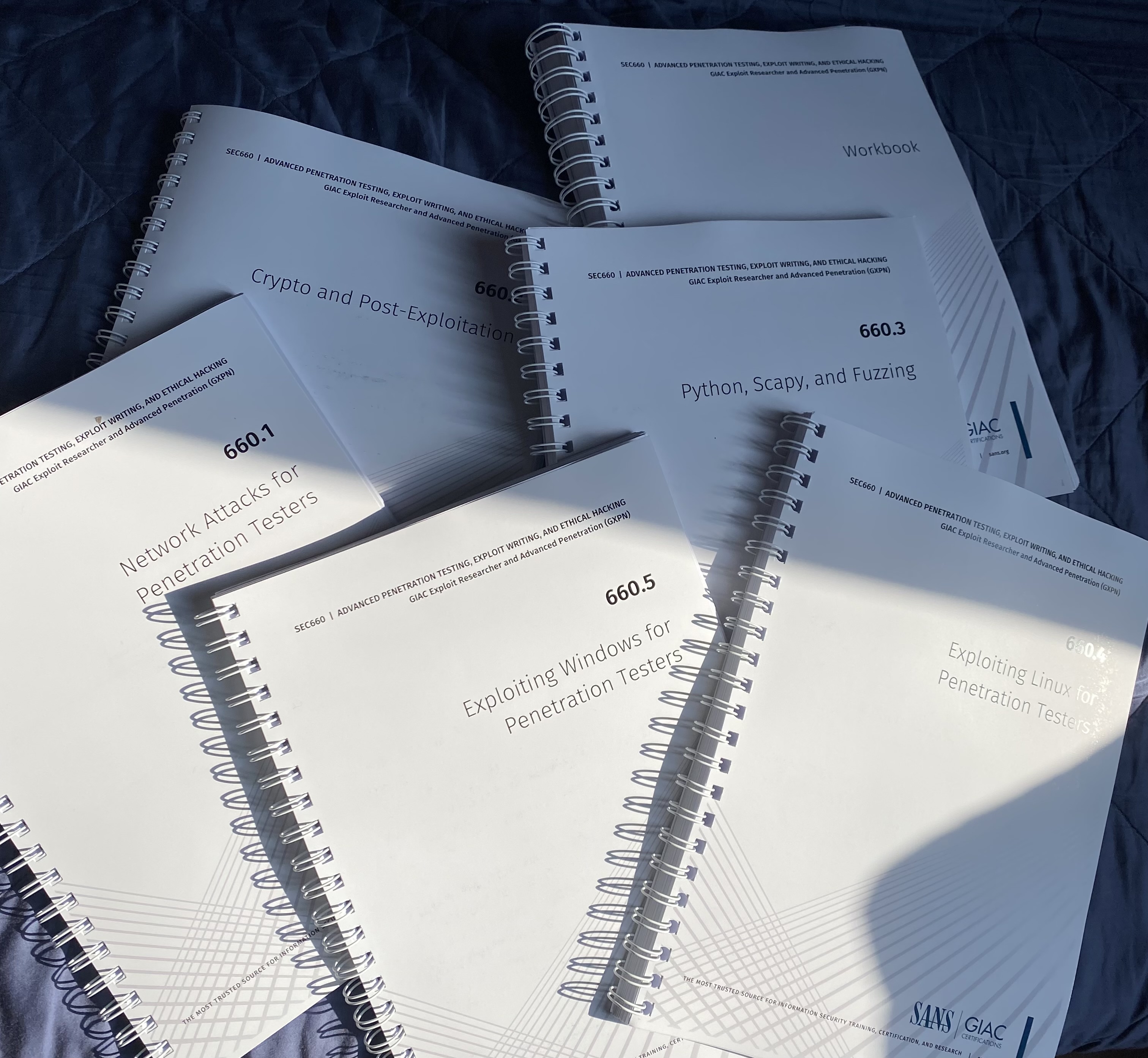
Once signed up, you get a big box full of paper material in the post - 6 ring binders: one for each module plus a workbook.
These contain all the slides from the lectures, with extra notes and explanation. You also get a downloadable disk image containing 3 virtual machines - Windows, Ubuntu and Slingshot (SANS' own offensive linux distro), a VMWare Fusion download and student license. Plus a couple of VPN profiles for live exercises on real remote machines.
The materials say you should run everything on Windows or MacOS and they don’t support Linux. However, I ran everything on Ubuntu 23.04 without a single problem.
Content
There are 5 modules, each containing about 4 - 6 hours of video lectures, with a practical exercise after each topic and quiz and bootcamp at the end of every module. Then it’s capped off with a course-wide CTF and a 3 hour proctored exam (if you chose the certification path on signup).
The course authors are Jim Shewmaker and Stephen Sims and they do a fantastic job of explaining everything in a clear, concise way - but also often quite informally, as you might explain it to a friend. This last point really helps for me personally as it’s way better to hear info like that than read it in a dry textbook. Simple, clear, accurate, complete but without unneccessary complications (even when the content gets quite complex later in the course).
I’ll go through some of the course content below, highlighting the stuff I found most interesting in each module.
1) Network Attacks for Penetration Testers
This module featured many techniques to manipulate and exploit local network protocols and bypass controls like AMSI. There was a section on bypassing Network Access Controls and captive portals with an array of different tools and techniques.
For example, plugging into the local network, sniffing with Wireshark and inspecting the traffic between your machine and the captive portal itself - asking ‘how is this portal profiling me? Is it fingerprinting the OS, browser, open ports on my machine?’ etc. Then spoofing the desired traits to gain access. Or accessing the wifi network by impersonating an employee who has recently left the building but hasn’t logged out of their session.
Once the network is accessed, it covered ways to manipulate the traffic to gain credentials or higher privilege access. E.g. credential theft via ARP spoofing. Or by manipulating routing protocols like OSPF or HSRP. It looked at IPv6 and how misconfigurations can be exploited, as well as other LAN-based attacks like SSL stripping.
The nice thing about this module was it covered a lot of techniques and technologies, yielding an arsenal that allows an open-ended approach; meaning you can plug into a network, see what protocols or controls are in use, and most likely have something to work with. And while some of the attack prerequisites might seem a bit far-fetched, I’ve since encountered a few on engagements, which is a testament to how useful this course is.
2) Crypto and Post Exploitation
This module is one of the main reasons I wanted to do this course. I think for many testers, the Crypto area of the OWASP testing guide is one of the scariest and least explored. Plus, studying cryptography is often so dry and theoretical and I was hoping for practical, offensive-focused content. The course delivered - there was an introduction to how various stream and block ciphers work followed by practical attacks.
It detailed how to assess the security of encrypted material you find on engagements - is it actually encrypted, not just encoded/obfuscated? What algorithm is used? It showed how to visualise data in histrograms and measure the entropy. CBC bit flipping, oracle padding and stream cipher IV reuse attacks were covered.
Honestly, I do feel like I’m unlikely to find the prerequisites to carry out most of these attacks on real engagements (e.g. a server that discloses a padding oracle to the client) but after this course I feel a lot more confident in analysing crypto in the wild and will definitely use these techniques as the opportunity arises.
The post exploitation section of the module focused on offensive powershell, escaping kiosks, bypassing EDR and some use of C2 frameworks. A lot of the techniques here were covered in OSCP but it added some extra tips, tools and considerations which was useful.
3) Python, Scapy and Fuzzing
Probably the lightest module, it started off with some handy python tricks for manipulating data types and exploring Portable Executable files with the pefile library. Then it went into using scapy for packet manipulation and fuzzing with sulley.
It looked at how to fuzz binaries with or without access to source code using DynamoRio and AFL.
Some interesting techniques here and as they say in the course, fuzzing is something you can always have running in the background while doing manual testing. Probably the least useful content for day to day engagements personally, but great for running in the background and more focused application testing.
4) Exploiting Linux for Penetration Testers
This is where the technical level started to ramp up. We started with details of memory in general, from the very basics - particularly focusing on the various processor registers and what they do. Mostly 32-bit focused but including 64-bit explanations where they differ.
Then virtual memory and paging was explained. Then stack operations - push, call, procedure prolog and epilog - all explained step-by-step and with clarity. GDB and the python exploit development assistant are used throughout. There’s a lot of assembly from this module onwards. Single and multi-stage shellcode was explored, including how to test that it’s actually doing what it should, which is a wise thing to do before launching payloads in production.
There were a few labs that explored stack overflows of increasing difficulty. Using Return Oriented Programming, ret2libc and finding the right gadgets for these techniques.
One of the most fascinating aspects of this module and the next was studying the various memory protection schemes and bypassing them one by one. Stack canaries and ASLR were explored here. For someone like me who spends very little time in a debugger, it can seem so inscrutable, but the course takes you through the basics and sheds some light.
5) Exploiting Windows for Penetration Testers
This was more of the same, but Windows-specific. Looking at the PE/COFF format, how loaders and linkers work, the Windows API. The formula of giving students a really brief overview then focusing on what you need to know for attacks works really well. For example, the Windows API was explained briefly, then there was a laser focus on the Thread Information Block and Procecss Environment Block, and the stepping stones you need to skip over to load a library of your choosing in your exploits.
Here, Windows-specific mitigations were explained, as well as how to bypass or brute-force them. These included SEHOP, Stack Canaries, PEB Randomisation, Hardware DEP etc.
The Exam
It’s a 3 hour, remote, proctored exam with 60 questions. Open book. The proctors are quite stringent in checking everything - they want to see all around your room, that you’re not wearing any earbuds, the front and back of each book, underneath each book on the table etc. I think just the setup took around 15 mins. The questions are mostly multiple choice with a few practical tasks in VMs.
I won’t say anything specific to avoid breaching integrity rules but advice that I received (and that paid off) was to spend some time making an index of all topics, tools etc. so you can find answers quickly. Some of the questions are written in a way that is a bit tricky - so you should be able to double-check your answer quickly if you need to. I took the whole 3 hours and passed with 85%.
Overall Thoughts
SEC660 was a great experience for me. It demystified a few murky corners of my knowledge and experience and made me feel better equipped to do a wide range of engagements. I immediately began incorporating stuff I was learning into my workflow. I studied maybe 4-8 hours a week on average and took the full 4 months allowance, and it felt a very relaxed pace. I highly recommend it for someone with previous certs looking to dig deeper on some of the topics mentioned above.
Thanks for reading! For any questions or comments, feel free to get in touch.